Executive summary — leaked ICE contracts could spotlight vendor surveillance risks amid DHS shutdown
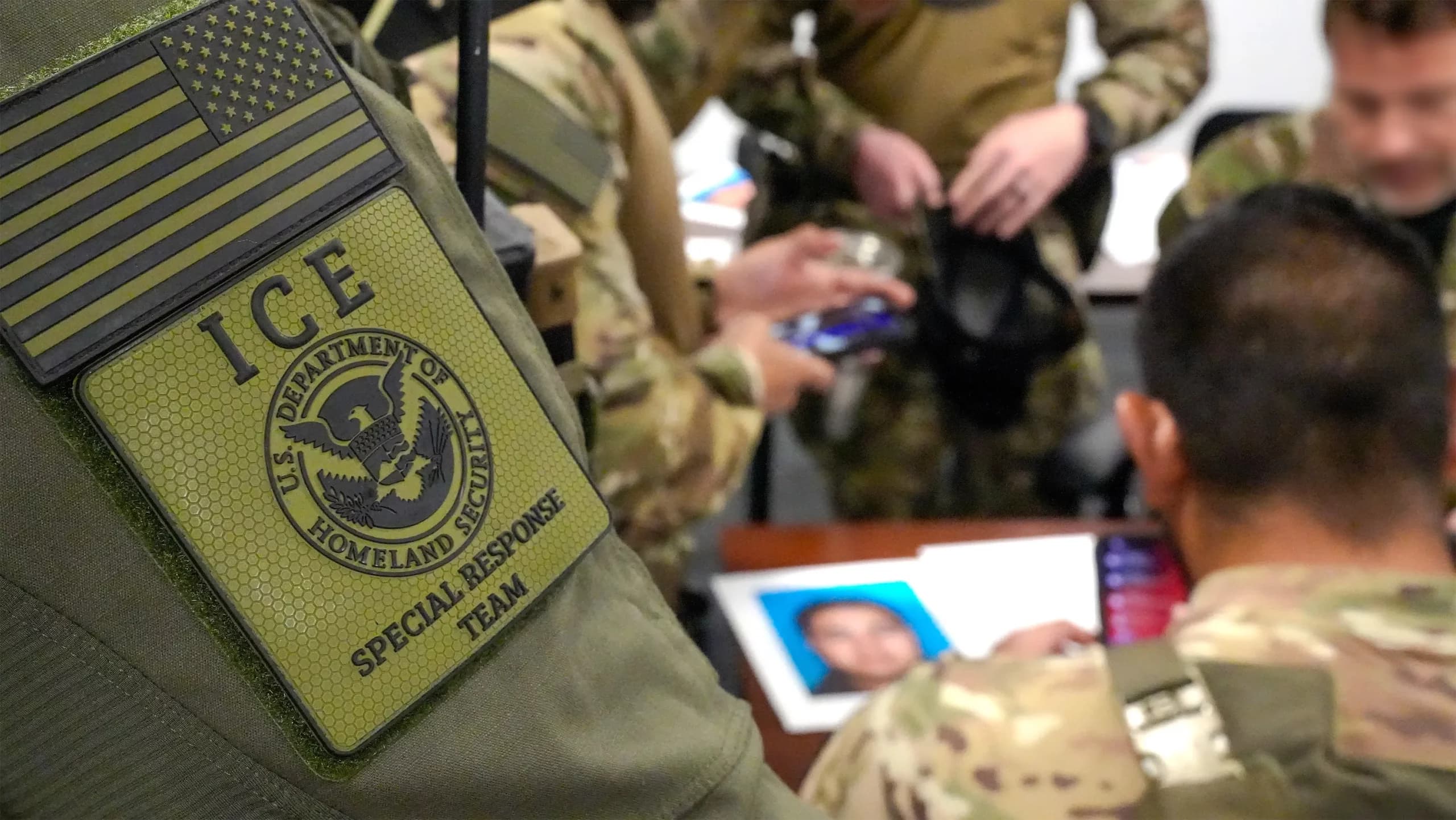
The alleged breach of Department of Homeland Security systems, if validated, would expose the concentration of third-party surveillance providers and highlight oversight gaps intensified by the concurrent DHS partial shutdown.
- Immediate impact: Public disclosure of contractor identities, contract values, and program specifics tied to surveillance and data-collection tools could fuel adversary targeting and social-engineering campaigns.
- Quantified risk vectors: Reported contracts include a September 2025 $2.3 million PenLink award, public filings indicate multimillion purchases from Venntel and Babel Street, and prior investments in Cellebrite ($11 million) and Clearview AI (~$10 million).
- Governance gap: Congressional calls for inspector general probes could intensify as a DHS operational slowdown likely delays federally required cyber incident reporting to CISA and curtails timely oversight.
Breaking down the TechCrunch claim
Hacktivists, as reported by TechCrunch on March 2, 2026, claim to have extracted and released ICE contract records. No DHS, ICE, CISA or independent cybersecurity firm has publicly confirmed the dump’s authenticity, scale, or technical provenance. That absence of verification is material—unvalidated data dumps can misattribute sources or overstate programmatic impact.

Why this matters now
Two concurrent factors amplify the claim’s significance. First, more than 70 House Democrats have urged an inspector general probe into surveillance-related contracts following oversight concerns and past compliance lapses. Second, the DHS partial shutdown that began the week of March 2 may stall legally mandated or recommended incident reporting, delaying external notifications and congressional briefings.
Concrete details and risk quantification
Public records and advocacy filings illuminate why these contracts carry sensitive surveillance capabilities. Examples cited in public filings include:
- A September 2025 $2.3 million contract with PenLink for warrantless location-tracking and internet analytics tools.
- Venntel purchases exceeding $2 million in 2019-2020 for bulk cell-phone location data brokering.
- A $3 million renewal with Babel Street in 2020 for geofencing and cross-border tracking services.
- Reported multimillion-dollar investments in Cellebrite phone exploitation tools ($11 million) and Clearview AI biometric face recognition (~$10 million).
Past vendor incidents—such as a 2025 supply-chain exposure involving a contractor handling LexisNexis/Accurint data—demonstrate how third-party compromises can leak personally identifiable information affecting federal personnel.
Operational and compliance implications
- Procurement exposure: Contract details could reveal which vendors have privileged access to surveillance tooling and under what terms, creating a roadmap for adversarial intrusion attempts or disinformation tactics.
- Incident reporting: DHS operational constraints during the partial shutdown may delay notifications to CISA and other agencies, heightening regulatory and reputational risk if a breach is later confirmed.
- Oversight pressure: Existing congressional and inspector general inquiries into surveillance contracts could expand to scrutinize vendor security practices and lifecycle controls.
How this aligns with past vendor breaches
Government reliance on external data-collection firms and surveillance tool providers has repeatedly produced concentrated risk. The 2025 LexisNexis/Accurint breach exposed over 360,000 records and underscored systemic vendor control weaknesses. The current claims follow this pattern, though no independent sample files or technical logs have been published to date.
Potential verification signals
- Official DHS, ICE or CISA statements acknowledging the breach would signal formal recognition of the incident.
- Independent validation from established cybersecurity firms—through IOC releases or file-level sampling—would clarify the authenticity and scope of the dump.
- Expanded activity by congressional committees or the DHS inspector general into contract governance could reflect intensifying oversight driven by the leak’s fallout.