Find Hub hands airlines device‑sourced coordinates — a shift of power, process, and privacy in lost‑bag recovery
Android’s Find Hub URL sharing shifts the locus of lost‑baggage recovery from manual reporting to device‑sourced coordinates, changing airline operations and privacy responsibilities.
Executive summary — what changed and why it matters
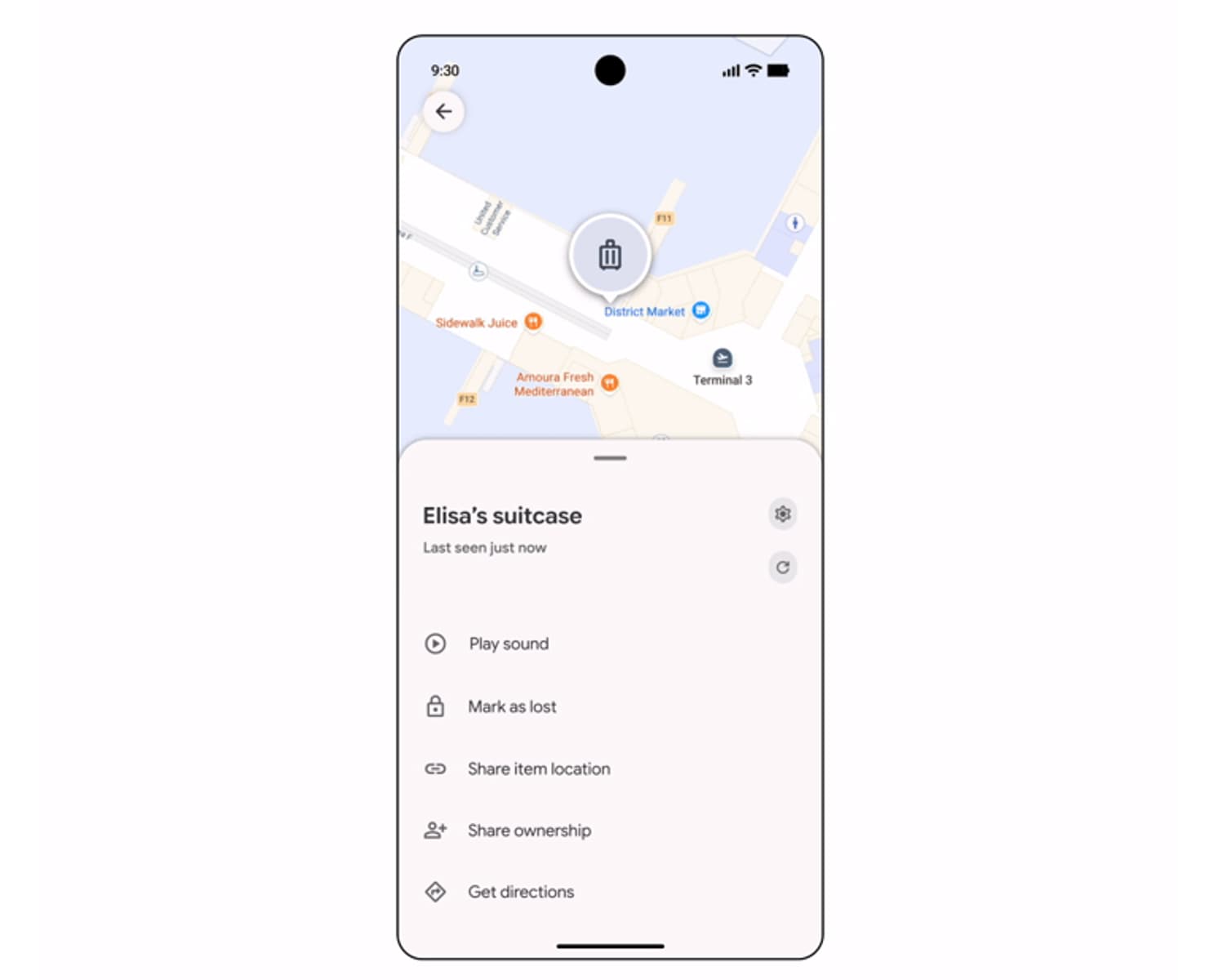
Google’s March 3, 2026 Pixel Drop introduced an integration that lets Android users generate a secure, expiring URL from the Find Hub app and paste that link into airline apps or web forms so carriers can use device‑reported coordinates to locate lost luggage. Google’s Pixel Drop summary describes the link as one that “auto‑expires after seven days or when the item is marked reunited” and characterizes the shared location data as protected by “end‑to‑end encryption.”
At launch, more than ten airlines are reported as initial partners, explicitly including Ajet, Air India, China Airlines, the Lufthansa Group (Lufthansa, Austrian, Brussels, Swiss), Saudia, Scandinavian Airlines, and Turkish Airlines, with Qantas support planned. Google is also working with Samsonite to embed Find Hub compatibility into new suitcases while continuing support for third‑party Bluetooth trackers such as Chipolo.
How the feature actually works (as reported)
The operational flow reported in early coverage is straightforward: a passenger marks a compatible tracker as lost inside Find Hub; Find Hub generates a unique URL tied to that tracker’s location stream; the passenger provides that URL to an airline via a lost‑and‑found form or app. The link is described as short‑lived — Google’s summary gives seven days as the expiry window and notes automatic termination when the item is marked reunited — and the company reports that the link shares location data with “end‑to‑end encryption.”
There is at least one conflicting claim in the early reporting cycle: a source cited a 24–48 hour expiry. Primary reports and Google’s Pixel Drop language align on seven days, but the discrepancy highlights the absence of a single, detailed developer changelog or dedicated technical blog post in the initial coverage. That gap makes certain implementation details — for example, whether airlines receive continuous updates while the link is active or only a last‑seen coordinate — unclear until official developer documentation or API notes are published.

Operational reality for airlines
The visible shift is procedural: passenger accounts and free‑text descriptions have long been the starting point for lost‑baggage searches; Find Hub changes the starting point to a piece of machine‑generated evidence — a URL that resolves to device‑reported coordinates. That alters who controls the primary signal in a recovery workflow and how quickly an operation can triage a claim.
Concretely, airlines that accept Find Hub links gain access to what is framed as device‑sourced locational certainty. In practice, that will affect triage logic, routing of tasks, and the division of labor between customer service desks, baggage handlers, and centralized operations centers. It also creates new dependencies: carriers will need parsers or ingestion routines to validate a link’s integrity, systems to translate coordinates into physical search actions at a particular terminal or carousel, and procedures for reconciling device data with human verification — for example, when a device‑reported coordinate points to a public space rather than a secure airport zone.
Because much of the rollout is with non‑US majors in the initial partner list, the operational case for global carriers will unfold unevenly. The scale‑dependent benefit — fewer hours spent chasing ambiguous customer descriptions — depends on two adoption axes: how many airlines finish integrations and how many passengers use Find Hub‑compatible trackers.

Privacy, identity and the redistribution of power
At the human level, the integration reassigns informational power. Instead of airlines relying on passengers’ descriptions and staff reconnaissance, carriers receive device‑sourced coordinates that can be acted on more directly. That redistribution has several social and regulatory implications.
- Agency and consent. The feature presumes active passenger consent at the moment of link generation, but the lifecycle of that consent — how it is recorded, revoked, or audited by carriers — is not yet codified in public documentation. Google’s Pixel Drop summary frames the link as expiring and encrypted, but whether airlines log access events or how they prove a passenger’s permission to use the coordinate remains an operational and legal question.
- Identity verification. Device coordinates can point to a location, but carriers must still tie that location to a lawful retrieval action and to the rightful owner. The shift from narrative claim ( “my bag looks like…”) to location evidence ( “last seen at…”) changes what counts as proof and who has authority to act on it. That authority has real consequences for passengers’ agency over their property and the employee discretion exercised when acting on device data.
- Surveillance and misuse. The technical protections reported — expiring links and end‑to‑end encryption — narrow a class of risks, but they do not eliminate misuse scenarios. If airlines retain locational logs or if ingestion flows lack strict validation, location sharing could be repurposed for stalking, unauthorized tracking, or intrusive operational practices. The risk is both individual (a passenger’s safety) and institutional (an operator’s exposure to regulatory enforcement or civil claims).
Legal and compliance contours
Because the integration involves personal data with precise location content, existing data protection frameworks are implicated. The European Union’s rules and some U.S. state laws treat location as sensitive data; regulators require documented lawful bases, retention limits, and data‑protection impact assessments in many cases. The absence of a detailed developer changelog in initial reporting means airlines and privacy teams are left with three immediate unknowns: the exact schema of data delivered via the URL, the server‑side entitlements carriers must assert to retrieve updates, and whether Google’s described encryption model leaves carriers with plaintext coordinates or only abstracted pointers.
How carriers answer those unanswered questions will affect cross‑border data transfers, incident response policies, and the appetite of insurance and legal departments to permit automated operational actions based on device coordinates.
Competitive and ecosystem effects
Technically and strategically, Find Hub narrows a functional gap with Apple’s 2024 AirTag airline sharing. But the ecosystem consequences are nuanced. Android’s approach — built around Find Hub and supporting a range of third‑party trackers plus hardware partnerships like Samsonite — broadens hardware choice, while differences in device population, carrier adoption, and tracking‑network density will determine how effectively the feature changes recovery outcomes.

For luggage and tracker manufacturers, the partnership model introduces product design tradeoffs. Embedding Find Hub compatibility into suitcases increases out‑of‑the‑box utility for travelers, but it also cements reliance on Google’s sharing model for lost‑item resolution. That creates commercial leverage for platform owners and shifts responsibility for interoperability and security into the supply chain.
Reliability and evidence gaps
Several pragmatic questions remain open in the public record. Early coverage indicates that Find Hub links are short‑lived and encrypted, but the documentation needed to assess real‑world efficacy — whether the link provides continuous, live updates, the frequency and precision of coordinates, and how quickly airlines can convert a coordinate into a physical search — is not yet available in a single authoritative form. One report’s 24–48 hour expiry claim conflicts with Google’s seven‑day statement; primary reports and Google’s Pixel Drop language align on seven days, but the discrepancy spotlights the reporting gap.
Until developer docs, API specifications, or airline operational reports appear, recovery success rates and average time‑to‑reunification remain untested metrics. Early adopters’ post‑deployment data will be decisive in determining whether device‑sourced coordinates materially reduce baggage loss durations or merely shift effort into new technical and governance practices.
Implications — likely effects, tradeoffs and risks
- Operational reallocation: Accepting device‑sourced coordinates is likely to accelerate initial triage, but it also reallocates work into validation, mapping, and physical search execution. That tradeoff shifts resource needs from customer‑facing narrative handling toward backend ingestion and field operations.
- Data custody and accountability: If airlines retain location logs, their exposure to data‑protection obligations and legal requests increases. Conversely, ephemeral or pointer‑based models reduce custodial burden but limit auditability and the ability to defend actions taken on the basis of location data.
- Power asymmetry: Platform owners and device ecosystems gain leverage when operational recovery depends on their data models. Hardware partners and tracker makers could extract commercial or policy concessions as their artifacts become central to reunification workflows.
- Regulatory friction: Differences across jurisdictions in how location data is regulated will make a single global operational model difficult. Carriers operating across borders will face inconsistent obligations and potential friction with passengers over consent and retention practices.
- Abuse scenarios and employee discretion: The move to machine evidence reduces some ambiguity but raises new abuse vectors if ingestion lacks rigorous validation. Human discretion at the moment of action — whether to retrieve an item from a public area, demand additional identity proof, or hand property to an agent — becomes the focal point for harm or error.
What to watch next
- Publication of Google developer documentation or a Pixel Drop changelog that fully describes the data model, update cadence, and security assertions for Find Hub airline links.
- Early operational reports from partner airlines about conversion rates (link received → bag found), false positives, and the interplay between device coordinates and physical retrieval efforts.
- Regulatory and civil‑society scrutiny of carrier retention policies and abuse controls, especially in jurisdictions with stringent location‑data protections.
- Expansion of the partner list to US majors and the behavior of embedded hardware from luggage manufacturers in real‑world deployments.
Conclusion
Find Hub’s airline integration reframes lost‑baggage recovery as a problem solved in part by device‑sourced coordinates rather than only by human narrative and manual search. That reframing redistributes operational responsibility and informational power, bringing efficiency gains into tension with legal, privacy, and social risks. The net effect will depend on engineering details still absent from public developer documentation, airline adoption patterns, and how regulators and affected communities address the new locus of locational authority.