Executive summary – what changed and why it matters
The LeakBase takedown is a tactical win that constrains public access to commodified credentials but is unlikely to stop the market absent follow-on actions across hosting, payments and buyer networks.
Key takeaways
- Impact: Authorities removed a marketplace that scaled credential theft and resold cybercrime toolkits, potentially reducing easy access to “combo lists” and automated attack kits.
- Scope & limits: Takedowns disrupt public availability but do not erase compromised data already circulating or halt private trade in closed forums and encrypted channels.
- Precedent: Similar international operations (Hansa/2017, Genesis/2021) delivered short-term disruption but often led to fragmentation rather than elimination of trade.
- Uncertainty: Public reporting so far omits quantitative details on seized assets and investigative partners, complicating precise risk assessment.
- Enterprise responses: Organizations typically verify exposures, rotate credentials after confirmed leaks, enforce phishing-resistant MFA, and deploy enhanced monitoring for credential-stuffing activity.
Breaking down the action
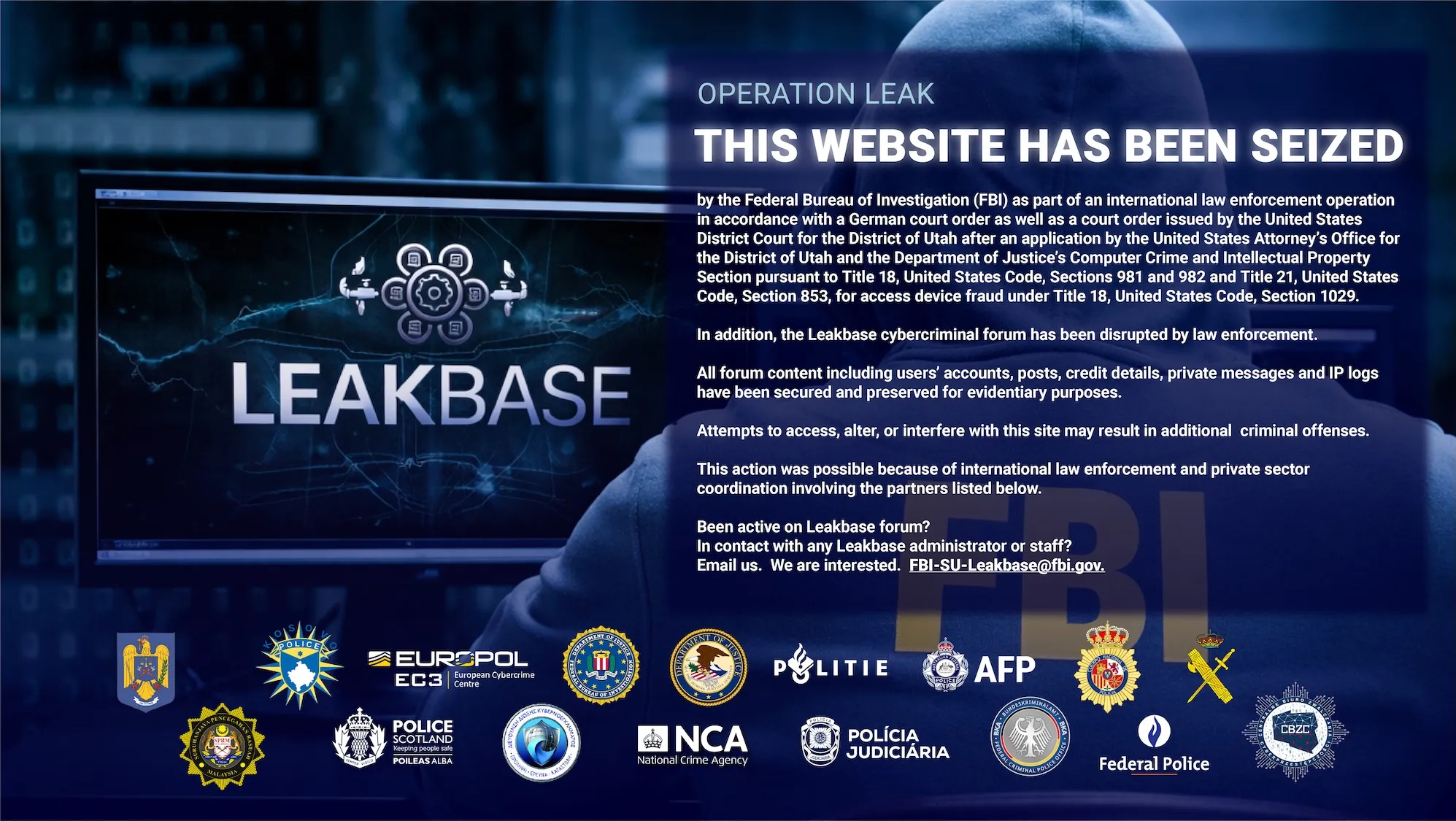
U.S. and EU law enforcement coordinated a cross-border operation that took the LeakBase site offline, employing domain seizures, hosting disruptions and asset freezes. Reports reference an extended investigative phase preceding the takedown, reflecting growing operational alignment under mutual legal assistance frameworks.
The stated aim was to disrupt a hub for stolen credentials and cybercrime tools that facilitate account takeovers, fraud and large-scale bot attacks. Details on arrests, forensic evidence captured or physical server seizures have not been publicly disclosed, leaving open questions about the full scope of data removed from circulation.
Why now – policy and market context
This action aligns with a multi-year trend of intensified international cooperation against cybercrime marketplaces and heightened regulatory scrutiny. Regulators and law enforcement have increasingly targeted platforms that accelerate credential theft, leveraging pressure on hosting providers, domain registries and payment rails alongside evolving policies such as the EU’s Cyber Resilience Act and U.S. executive directives on supply chain security.

In parallel, industry initiatives have pressed infrastructure providers to adopt anti-abuse measures, from automated threat-intelligence sharing to stricter vetting of domain registrations and payment-processor compliance programs.
Observed effects on defenders and buyers
Among security teams, the most immediate observed effect is a decline in publicly advertised credential-list availability. Historical precedents suggest temporary reductions in automated credential-stuffing attempts, though public data on the duration and scale of this effect from LeakBase’s takedown remains unavailable.

Some threat-intelligence providers have noted anecdotal drops in credential-stuffing alerts, but attribution to this operation is unverified. Two persistent dynamics endure: once leaked credentials are in circulation they continue to be useful, and threat actors often migrate to mirror sites, closed forums or encrypted messaging platforms, complicating long-term visibility for defenders.
Risk and governance considerations
Legal and compliance teams often regard cross-border enforcement as raising the frequency of evidence-sharing requests and setting new precedents for domain seizure under mutual legal assistance treaties. Debates persist around data sovereignty and evidence handling, given varying privacy and retention laws across jurisdictions.
Organizations managing breach notifications and regulatory reporting typically prepare for follow-up inquiries, with preservation of logs and coordination with incident-response providers becoming standard practice when investigations link leaked customer data to internal systems.

Competitive and historical comparison
This operation echoes earlier disruptions—the Hansa marketplace intervention in 2017 and the Genesis Market takedown in 2021. Each produced short-term supply constraints without dismantling the economic incentives underpinning stolen-data commerce. Post-Hansa fragmentation spawned multiple smaller forums with stricter access controls; the Genesis takedown drove activity into encrypted messaging groups and private channels. That pattern underscores the insufficiency of isolated takedowns to achieve enduring market collapse.
Common mitigations and strategic shifts
- Dark-web monitoring: Defenders often deploy continuous monitoring across underground channels to detect mentions of exposed domains or customer emails.
- Credential hygiene: Organizations frequently rotate compromised credentials and revoke active sessions following confirmed exposures.
- Multi-factor authentication: Phishing-resistant standards such as FIDO2/WebAuthn are increasingly enforced to mitigate unauthorized access risks.
- Credential-stuffing defenses: Industry practices include rate limiting, progressive delays, device fingerprinting and behavioral-anomaly detection to counter automated attacks.
- Identity modernization: A growing shift toward passwordless authentication and enhanced identity lifecycle management reflects strategic thinking about long-term risk reduction.
In sum, the LeakBase takedown removes a prominent public marketplace and complicates access to commodified credentials. Yet, in the absence of sustained follow-on measures across hosting, payments and buyer ecosystems, the underlying economics of credential theft are likely to persist through private and mirrored channels.